Network Activity Overview Linked to 1zy549vdwefaqwd54670 and Monitoring Notes

The network activity associated with identifier 1zy549vdwefaqwd54670 presents noteworthy patterns indicative of substantial data transfer. Recent monitoring highlights a pronounced increase in bandwidth usage, raising questions about its legitimacy. Anomaly detection mechanisms have identified several irregularities that could suggest unauthorized access. A deeper examination is necessary to determine the root causes of these fluctuations and assess potential vulnerabilities within the network infrastructure. Further insights may reveal critical implications for security measures and performance optimization.
Analyzing Network Traffic Patterns
When analyzing network traffic patterns, it becomes essential to identify the underlying behaviors and trends that define data flow within a network.
Traffic analysis facilitates the examination of data packets, revealing usage metrics and bandwidth consumption.
Through pattern recognition, analysts can discern normal operating conditions, enabling informed decisions that promote efficient resource allocation and enhance overall network performance, thus preserving user autonomy.
Identifying Anomalies and Potential Threats
How can network administrators effectively identify anomalies and potential threats within their systems?
Utilizing advanced anomaly detection algorithms, they can analyze deviations from established traffic patterns.
Regular threat assessment protocols, including behavioral analysis and signature-based detection, enhance the identification process.
This vigilant monitoring fosters a proactive approach, ensuring that administrators can swiftly mitigate risks and safeguard network integrity against emerging threats.
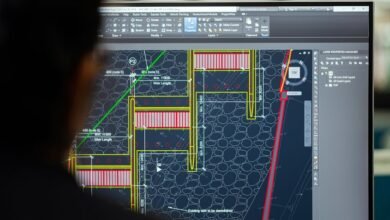
Performance Optimization Strategies
Effective performance optimization strategies are essential for maintaining network efficiency and reliability.
Implementing bandwidth management techniques ensures equitable distribution of resources, preventing congestion.
Additionally, focusing on latency reduction through optimized routing and efficient data handling minimizes delays, enhancing user experience.
These strategies collectively empower network administrators to sustain high performance, ultimately fostering a more resilient and agile network environment that supports user autonomy.
Recommendations for Enhanced Security
As network performance optimization strategies enhance resource allocation and user experience, the importance of robust security measures becomes increasingly apparent.
Implementing advanced user authentication protocols ensures that access is limited to authorized personnel, while employing data encryption safeguards sensitive information during transmission.
These practices create a resilient framework that not only protects user data but also empowers individuals with the freedom to navigate the digital landscape securely.
Conclusion
In conclusion, the comprehensive analysis of network activity linked to identifier 1zy549vdwefaqwd54670 underscores the critical need for vigilant oversight in the face of rising bandwidth consumption and detected anomalies. While some may argue that increased monitoring is burdensome, it is essential to recognize that safeguarding sensitive information and maintaining network integrity are paramount. By prioritizing performance optimization and robust security measures, organizations can foster a safer digital environment, ultimately protecting their users and preserving trust.