User Activity Documentation Linked to Keevee1999 and Alerts Logs
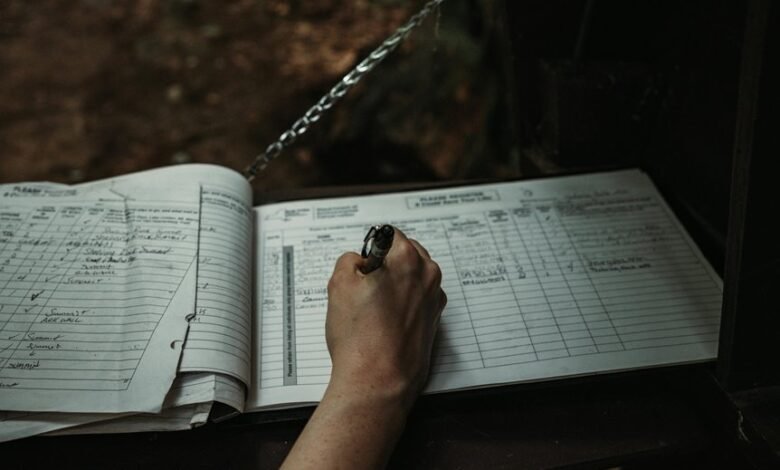
User activity documentation associated with Keevee1999 serves as a vital resource in the analysis of alerts logs. This documentation provides insights into user engagement patterns and potential security threats. By closely examining these records, security teams can identify trends and anomalies that warrant further investigation. Understanding these dynamics is crucial for effective risk management, yet many organizations struggle to implement best practices. This raises the question of how to optimize monitoring efforts.
Overview of User Activity Documentation
What constitutes effective user activity documentation? It encompasses meticulous activity tracking that captures user engagement patterns, facilitating a deeper understanding of behaviors.
This documentation serves as a vital resource, allowing organizations to identify trends, enhance user experiences, and optimize functionalities.
Analyzing Alerts Logs for Security Insights
Examining alert logs reveals critical insights into security dynamics within an organization.
By analyzing alert frequency, patterns of potential security breaches become evident. This data enables security teams to prioritize responses and identify vulnerabilities.
Furthermore, understanding the correlation between alert frequency and incidents can enhance proactive measures, ultimately fostering a more resilient security posture.
Such analysis is essential for safeguarding organizational freedom and integrity.
Patterns and Anomalies in User Behavior
While user behavior can often appear routine, identifying patterns and anomalies is crucial for enhancing security measures within an organization.
Behavior trends reveal normal activity, while unusual access may indicate potential security threats. Analyzing these discrepancies allows organizations to proactively address vulnerabilities, ensuring that freedom and security coexist.
Understanding these dynamics is vital for maintaining a secure digital environment in an increasingly complex landscape.
Best Practices for Monitoring User Activity
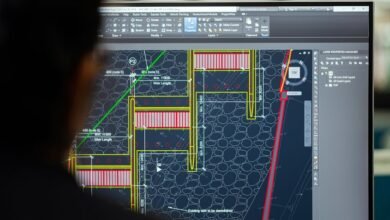
How can organizations effectively monitor user activity to enhance security?
Implementing robust activity tracking systems is essential for assessing user engagement. Regular audits, real-time alerts, and behavioral analytics enable organizations to identify irregular patterns and potential threats.
Additionally, fostering a culture of transparency encourages users to engage responsibly, thus reinforcing security measures while maintaining the freedom and privacy they value.
Conclusion
In the realm of cybersecurity, user activity documentation linked to Keevee1999 serves as a vigilant lighthouse, illuminating the turbulent waters of potential threats. As alerts logs unfurl their stories, they reveal the ebb and flow of user behavior, guiding security teams in their quest for safety. By discerning patterns and anomalies, organizations can navigate through the fog of uncertainty, fortifying their defenses and ensuring that the ship of integrity sails smoothly amidst the stormy seas of risk.